As described in “The How We Need Now,” a “concrete boat” is a project that’s doomed to fail from the outset due to misguided requirements and inappropriate processes. These problems are often visible during the solicitation process for new contracts. Seafaring vessels are christened; concrete boats are born into solicitation sin.
This is the next installment in our series on government solicitations gone wrong, in which we reveal common patterns and language in RFPs that should raise red flags signaling that a project is unlikely to deliver the intended outcomes — solicitation sins.
Each piece features examples posted on SAM.gov, the federal government’s bulletin board for advertising contract opportunities. We’ll also use the examples to teach a large language model how to identify solicitation sins, in order to estimate how common each sin is — and help contracting officers repent before they buy a concrete boat.
The series is based on the article “Alchemy for Aliens,” published on the author’s personal blog. You can read part 1 of this series on solicitation sins here.
Solicitation sin #3: Rule pools
Where should you look for concrete boats? At the bottom of Olympic-sized rule pools.
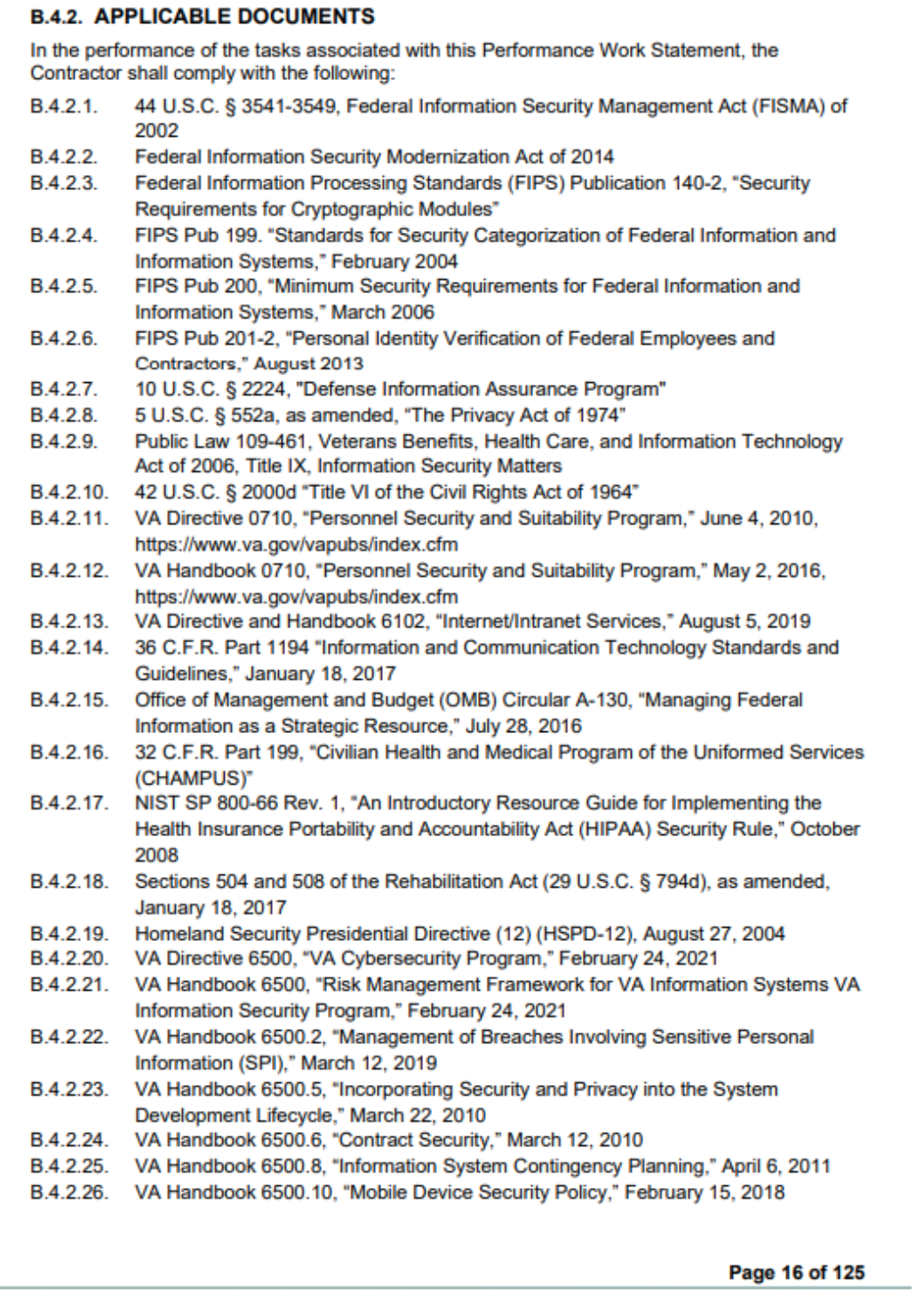
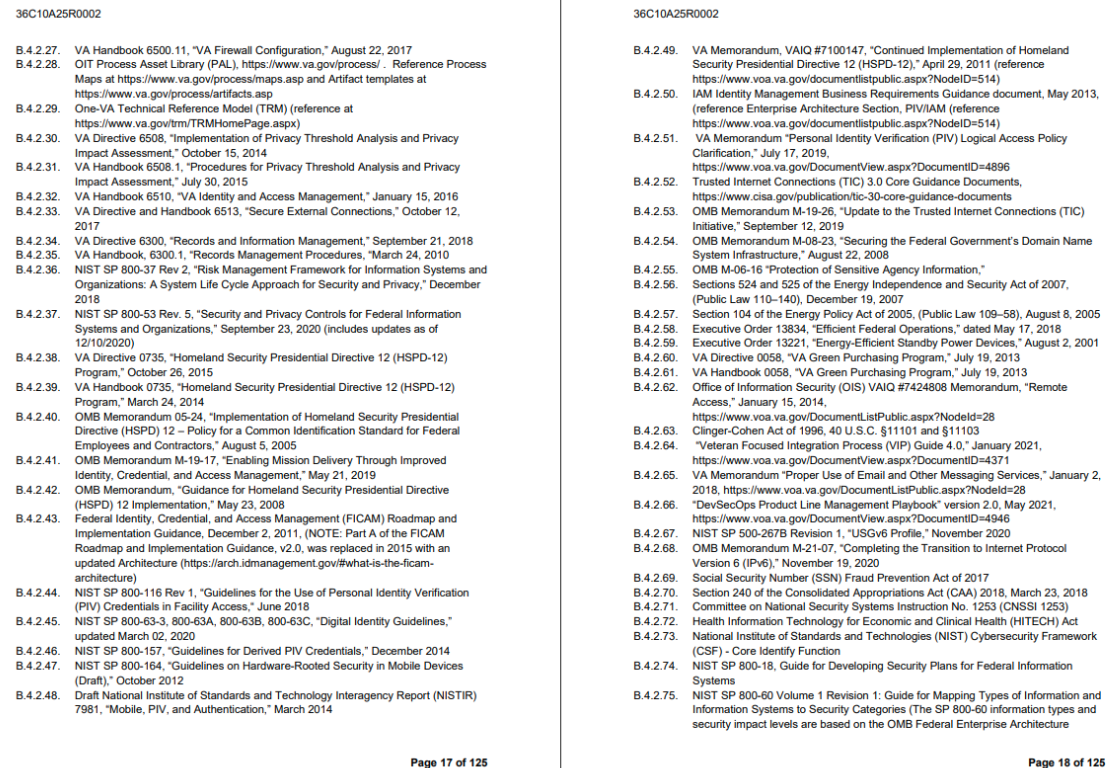
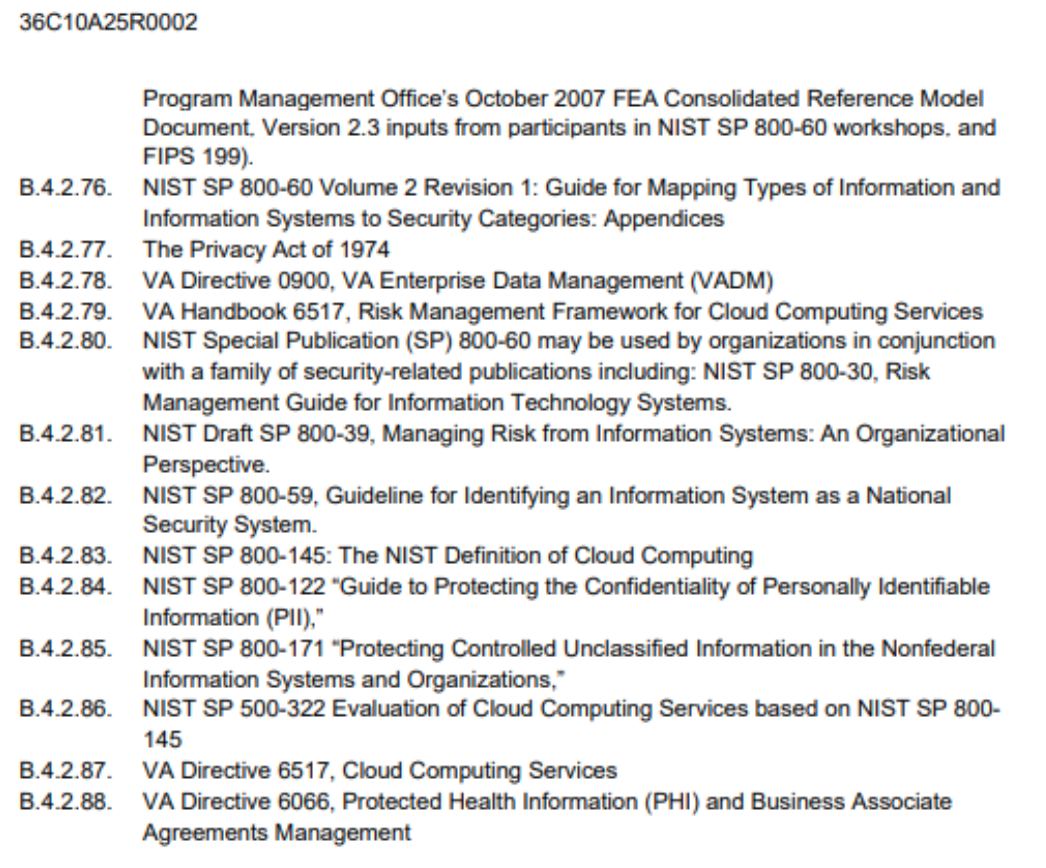
If you’d like to check out the rule pool for yourself, dive into the Department of Veterans Affairs’ recent request for proposals for a software system to send text messages. After two paragraphs of background, a potential vendor gets a handy list of 88 “Applicable Documents” that they must comply with. This includes, in its entirety, The Privacy Act of 1974; six separate policy documents about ID badges; and a 2001 executive order titled Energy Efficient Standby Power Devices.
Especially in IT solicitations, rule pools are surprisingly common: long lists of regulations cited without context. Solicitation writers can’t be blamed for the rules themselves, though higher-ups at the VA should consolidate many of those guidelines. But the rules apply whether they’re cataloged in the RFP or not. Presenting them in 88 undifferentiated citations obscures any that are germane to the product being built.
A great VA text message system needs to solve hard privacy and design challenges: How can nurses quickly and clearly share info about the dozens of patients they care for, while at the same respecting everyone’s privacy? Vendors could submit their best ideas for addressing these challenges, but the solicitation is more concerned about making them wade through a long list of “Applicable Documents.”
Besides obscuring novel compliance challenges, rule pools reflect passive management on the part of the agency that’s looking for a vendor. A good boss gets clarity for their team about ambiguous rules and pushes back when compliance overreach stops progress. But when the boss outsources rule reading to contracting officers and vendors, the result is a cascade of rigidity in which rules are applied more restrictively as they move down a hierarchy. When one of the 88 cited policies literally says, “VA personnel should not use SMS to conduct communications,”1 it’s easy to imagine a well-meaning engineer inventing bizarre workarounds to “comply” with an ambiguous guideline.
Since vendors have to pretend they understand all the rules, many will run away from intimidating rule pools, ultimately making the process less competitive.
‘Everyone into the rule pool!’
Rule pools fill up because leaders from Congress and the White House all the way down to individual program offices like the VA’s IT Office love to write rules. This growth has been likened to a cancer, and rule pools are proverbial lumps warning us to visit a doctor. An ongoing rewrite to the Federal Acquisition Regulations (FAR) will help in the long run — assuming FAR simplifications outweigh culture war campaigns like banning paper straws — but not in this case: none of the 88 policies cited above is actually from the FAR.
Given their limited technical know-how, government contracting offices often outsource responsibility to vendors for interpreting an ever-expanding catalog of IT regs. A contracting officer who leaves a rule out could be called careless. No one has ever been reprimanded, to my knowledge, for making a solicitation too long.
In a perfect world, new contracts would be a catalyst for revisiting old rules, not just an exercise in copying-and-pasting. “We’ve done the hard work of listing all 88 of these policies in one place. Now let’s see which ones are redundant!” If Congress is making the rules, nailing (or mailing) this list of 88 theses to the door of the House of Representatives might spark a legislative reformation. Lawmakers could size up their rule pools during legislative outcomes review to make sure their policy goals aren’t being drowned out.
Until then, solicitations should call out genuine compliance puzzles, ask vendors for their solutions — and then drain the rule pool.
Solicitation Sin #4: Insider rewards program
While the blame for rule pools lies elsewhere, contracting teams should head to confession for the next sin. It’s already difficult for “outsiders” to compete for federal contracts. When solicitations functionally exclude anyone who hasn’t won a nearly identical contract before, they’re not creating competition. They’re running an Insider Rewards Program.
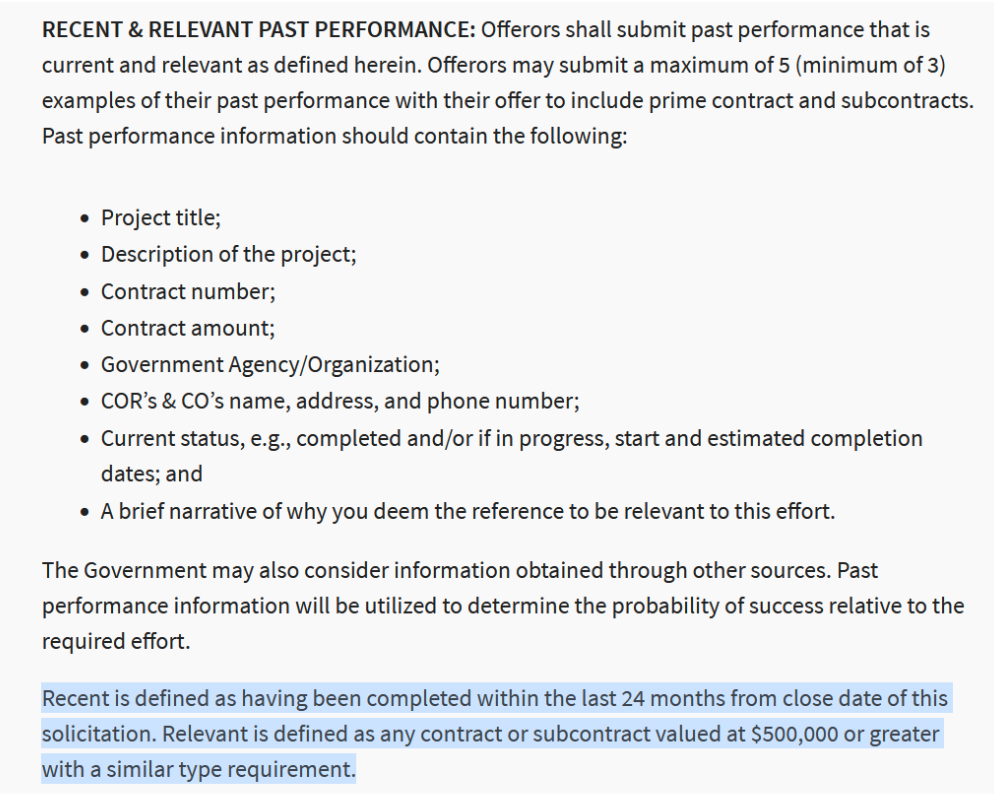
Examples abound, like a $25 million–$50 million Department of Defense construction contract — reserved exclusively for small businesses — for which program managers must have “five (5) years of experience managing Federal Government programs/contracts” (and 10 years total in administering contracts). Or a contract to update old Indian Health Service servers for which Native American-owned vendors need to submit three contracts each worth more than $500,000 for similar work in the past two years to show they’re qualified.
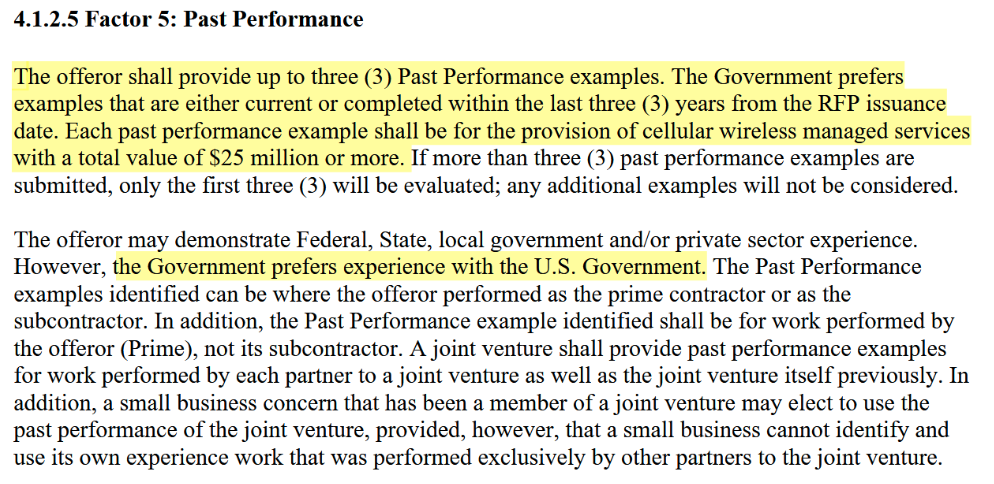
These types of requirements don’t generally benefit small businesses or new entrants: In bidding for the Department of Homeland Security’s $3 billion cell phone contract, businesses get extra points if they could show three $25 million cell phone contracts they’d won in the past three years.
Restrictions that favor “insiders” undermine faith that contracts are being awarded fairly. If outside vendors are excluded from the competition, the government will miss out on smart new approaches to fixing old problems.
In extreme cases, solicitations with Insider Rewards Programs could be plain corruption — the grievous sin of greed. Vendor capture is a more likely, or at least more common, explanation. As Matthew Burton writes, vendor capture happens
when a government agency becomes functionally dependent on a contractor or set of contractors to accomplish its mission. The dependencies go beyond basic support and extend into what are considered “inherently governmental” domains of knowledge, execution, continuity, and decision-making.
If your critical IT system is held together by duct tape, swapping out the insiders who do the duct taping for otherwise well-qualified competitors who haven’t duct taped is a hard sell.
Burton explains how agencies can solve vendor capture. One critical part of the healing process is excising RFPs of the arbitrary restrictions that amount to insider favoritism. Experience is undoubtedly valuable, but solicitations should give agencies the chance to weigh that experience against other benefits — new ideas or lower costs, for example — that “outsider” vendors can offer. Long-established procurement rules ensure the government won’t be forced to accept offers from unqualified upstarts who claim to be cheaper. In fact, they support creative evaluation methods such as coding tests or pilot projects.
It might seem risky to switch from the insiders you know, but the bigger risk is building concrete boats that sink services Americans rely on.
Solicitations should focus on hiring the best vendors and holding them accountable — exchanging Insider Rewards Programs for government services that benefit the public.
In the next article on “solicitation sins,” we’ll go below decks of the federal government’s concrete boats to peer into the machinery of contracting.
- Thomas G. Bowman, Deputy Secretary, “Proper Use of Email and Other Messaging Services” (official memorandum, Washington, DC: U.S. Department of Veterans Affairs, Jan. 2, 2018). ↩︎